Wake on LAN proxies – wake up remote PCs without using directed broadcasts.
Why WOL proxies
The WOL protocol only allows computers to be woken up in the local IP segment.
In order to enable remote computers to be woken up across network segments and even the Internet, the Auto Shutdown Manager Server offers two technically completely different approaches: Directed Broadcasts and WOL Proxies.
Directed broadcasts
The wake-up packets are sent directly to the endpoint router and triggered there as local broadcasts. However, this procedure is not permitted in most companies for security reasons.
WOL proxies
In practice, WOL proxies are used in the vast majority of cases. For this purpose, a computer or a device that supports Java, such as the Raspberry Pi, is configured in the remote network segment for continuous operation (24/7) and, if required, is instructed by the Auto Shutdown Manager server to wake up any computer that is relatively local to it via Wake On LAN. For example, it makes sense to use computers that are in continuous operation anyway (e.g. local servers) - or computers with the lowest possible energy consumption. In the case of smaller networks, this is easy to solve manually; for larger and more complex networks, the automatic generation of WOL proxies described below is useful.

Automatic WOL proxy generation and monitoring
The aim of the automatic WOL proxy generation, optimization, monitoring and maintenance is to ensure that the WOL server operates as reliable and maintenance-free as possible. The analysis can be run daily or according to your own schedule in order to identify changes in the network promptly and, if necessary, to optimize the selection of the WOL proxies fully automatically.
How the automatic WOL proxy generator works
The automatic search for suitable computers as WOL proxy takes place on the basis of a fully automatic analysis of the entire network infrastructure, including the computer types, their current runtimes, group membership and other settings, which are described below. The administrator can exclude unwanted computer types such as notebooks or purely virtual machines. Certain network segments can also be excluded from automatic proxy generation.
A filter allows entire groups to be excluded or treated as preferred. Preference is given to clients that are always on anyway.
A typical example of preferred groups are servers, if they have to run 24/7.
The administrators still have the option of manually determining individual network segments and WOL proxies. The administrator selection has the highest priority and is taken into account in the automatic generation and optimization.
In addition, the administrators have the option of defining a minimum segment size - otherwise it might not make sense to generate WOL proxies for very small segments with only 2 ... 3 clients.
If Raspberries or similar devices with the corresponding EnviProt WOL proxy drivers are used, these are automatically recognized and preferably entered as proxies.
A preview function gives administrators the opportunity to view the results in advance. For this, the generated proxy list is output as an Excel-compatible CSV file.
Optimization
During the network analysis, care is taken to optimize the number of WOL proxies to a minimum. This is achieved by detecting redundant subnets.
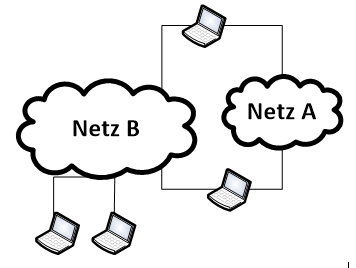
Example:
Network A is recognized as redundant and no WOL proxy is generated for it, as all clients can also be reached from network B.
On the other hand, it tries to determine computers that can serve several subnets.
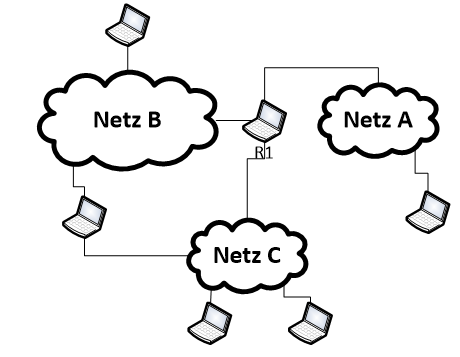
Example:
Computer R1 would be selected here because, as a WOL proxy, it can serve all three network segments:
Reliability
If a WOL proxy PC fails, the Auto Shutdown Manager server tries to find another currently running PC in the target network segment and promote it as a temporary WOL proxy. If the original WOL proxy PC does not respond for a certain period of time, it will automatically be replaced by the next best candidate. This guarantees a seamless and reliable WOL infrastructure without any administrative effort
Here you can find some more technical details and examples for Directed Broadcasts and for WOL Proxies.
Try Auto Shutdown Manager's WOL proxies to achieve the most reliable WoL solution across all your networks and VLANs.

 DE
DE  EN
EN